Introduction
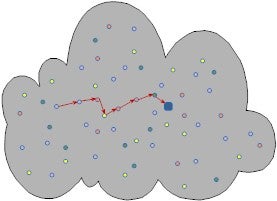
Wireless sensor networks (WSNs) are innovative networks consisting of a large number of distributed, autonomous, low-power, low-cost, sensor nodes which cooperatively collect information through infrastructureless wireless networks, as illustrated in Figure one. There are numerous applications for wireless sensor networks, and security is vital for many of them. However, WSNs suffer from many constraints, including low computation capability, small memory, limited energy resources, susceptibility to physical capture, and the lack of infrastructure, all of which impose unique security challenges and make innovative approaches desirable.
Preliminary results
Random Key Distribution for WSNs
Key establishment is one of most important building blocks for security services. Currently random key predistribution approaches are prevalent in wireless sensor network. We design a new key predistribution protocol which combines basic random key predistribution with multi-hash chain mechanism. Comprehensive analysis shows that its security performance outweighs that of original scheme, with reasonable tradeoff of a few hash operations.
Mutual Entity Authentication in WSNs
Mutual entity authentication plays a significant role in achieving many security goals of wireless sensor networks. We developed a mutual entity authentication framework for wireless sensor networks. This framework is basically flexible combination sets of two previous elegant one-way authentication protocols---HB+ and HB#, with significant enhancements in terms of infeasibility of storage/communication requirement and extension to mutual authentication.
Node Clone Detection
Sensor nodes lack tamper-resistant hardware and are subject to the node clone attack. We introduce two approaches to detect the attack distributively. One is based on Distributed Hash Table (DHT). A Chord overlay network is built upon the sensor network, and provides the key-based routing, caching, and checking facilities for our protocol. A deterministic witness and additional memory-efficient, potential witnesses assure the good security properties. Furthermore, the mechanism of random round seeds limits the adversary's ability to conceal the clone by compromising witness nodes. The other is an innovative randomly directed exploration protocol, which does not demand any strong assumptions and is highly practical in the general sensor network applications.